
Do You Think Your Lock Is Safe? Think Again…
Most of us trust the locks on our doors without a second thought. However, security research has shown that many commonly used pin tumbler locks have design limitations that may allow skilled attackers to bypass them more easily than most homeowners expect.
This blog is not meant to scare you, but to raise awareness about potential vulnerabilities in basic locking systems and explain why upgrading your home security can be an important step toward better protection.
Legal & Ethical Disclaimer
This article explains lock vulnerabilities for educational and security-awareness purposes only. Lock picking without explicit permission is illegal in many regions. This content does not provide instructions or encourage unauthorized access to property.
Why Pin Tumbler Locks Are Often Considered Vulnerable
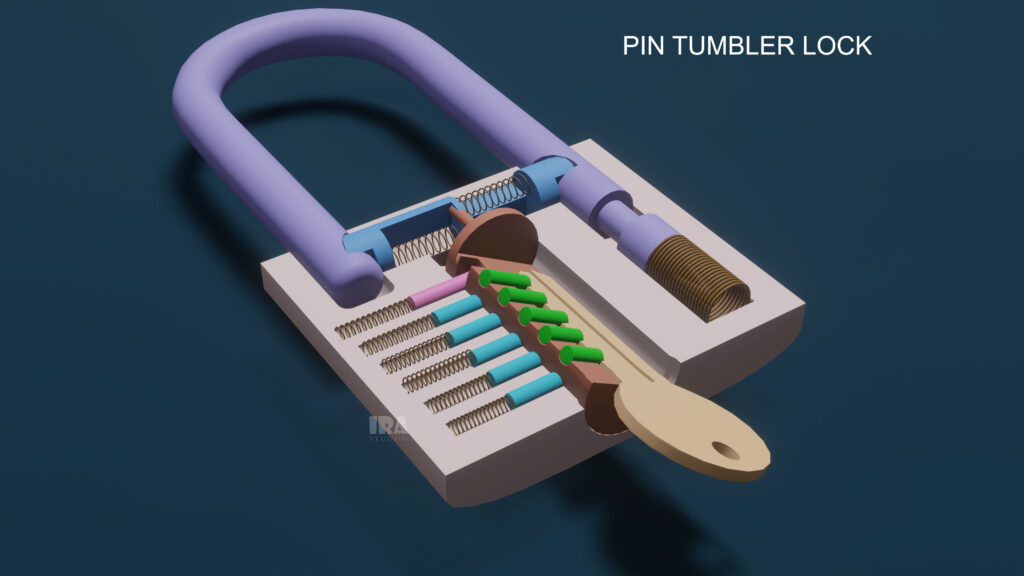
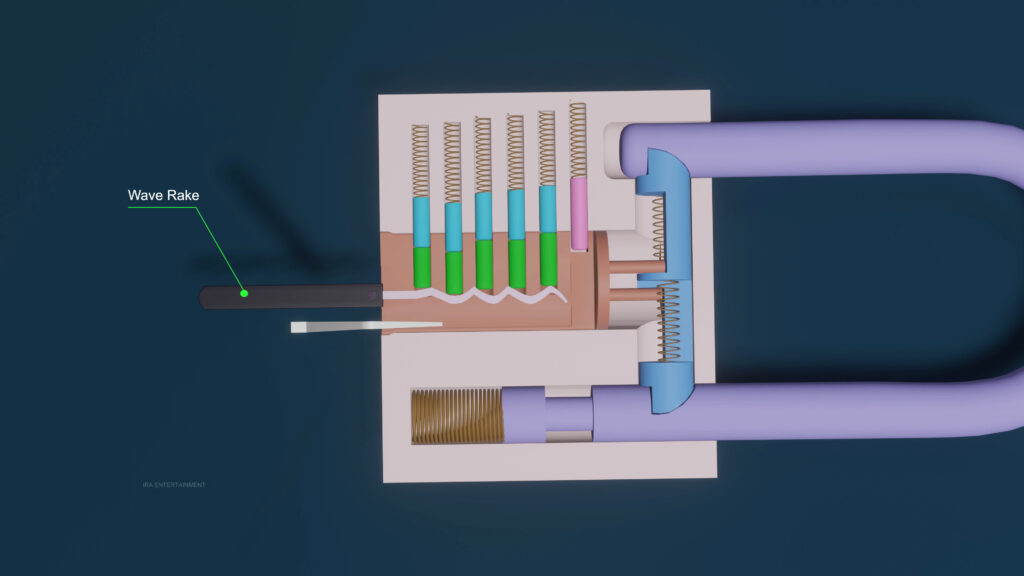
Pin tumbler locks are used in millions of homes worldwide and remain one of the most common locking mechanisms in use today. However, their popularity is partly due to their simple and standardized design, which also limits their resistance to certain forms of tampering.
These locks depend on internal components that must reach specific positions for the mechanism to operate. Because many pin tumbler locks are mass-produced, small variations in manufacturing can occur, which may reduce their overall resistance compared to more advanced locking systems.
Another contributing factor is standardization. Many basic pin tumbler locks share similar internal layouts, meaning they lack the additional protective features found in high-security designs. This simplicity, while cost-effective and reliable for everyday use, can make lower-end models less resilient against unauthorized manipulation.
Tools Commonly Referenced in Security Discussions
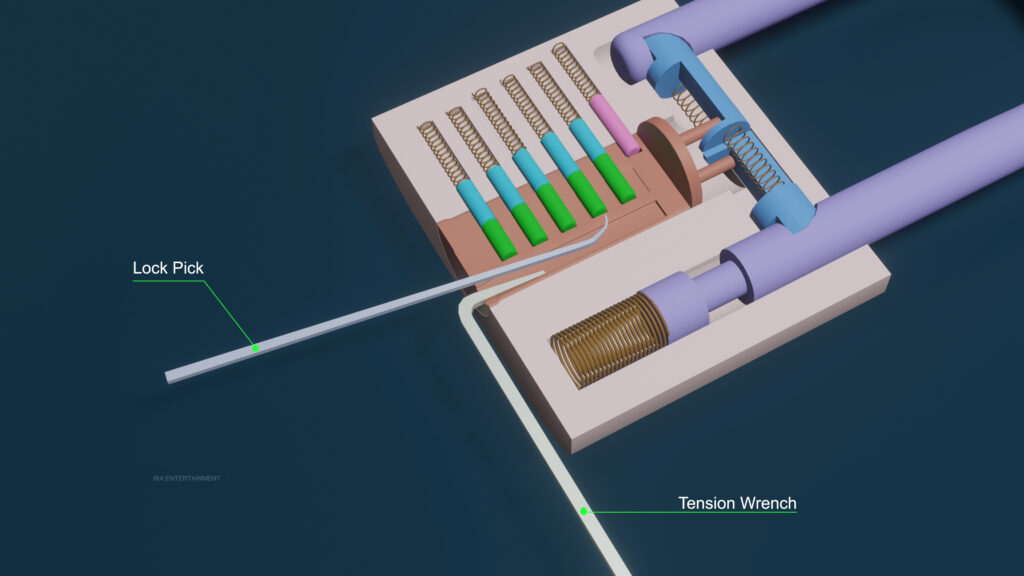
In discussions about lock security and vulnerabilities, certain tools are often mentioned to explain how basic locking mechanisms can be tested or evaluated. These tools are typically referenced in locksmith training, security research, or controlled environments.
Tension Tools: Used in security demonstrations to apply rotational pressure within a lock mechanism, helping researchers understand how internal components respond under stress.
Manipulation Tools: Thin instruments often referenced in educational materials to explain how internal lock components can be examined or tested during security assessments.
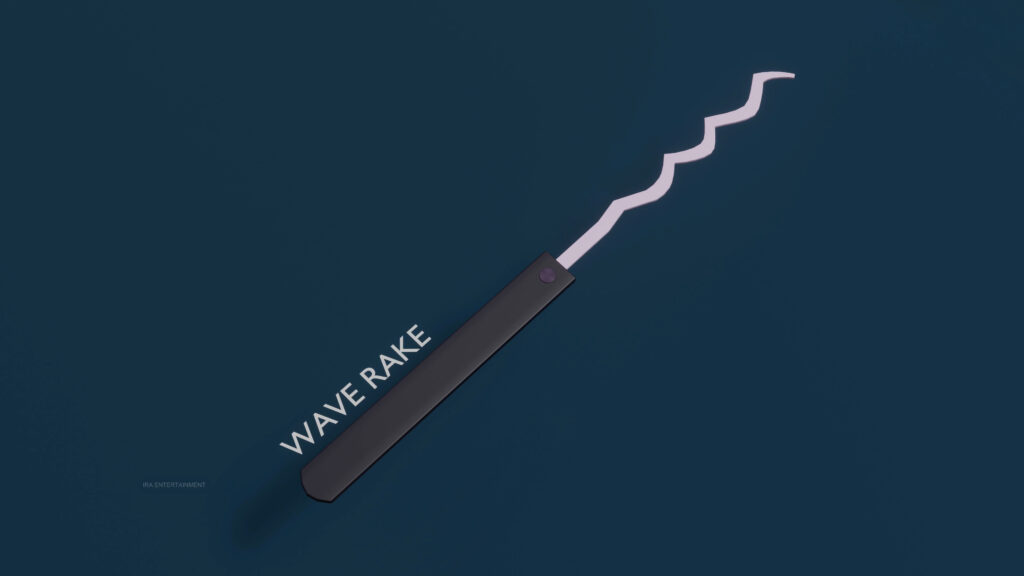
Raking-Style Tools: Frequently mentioned in discussions about low-security locks, these tools highlight how simpler locking systems may lack resistance to rapid internal disturbance, reinforcing the need for stronger designs.
Understanding the existence of these tools is not about using them, but about recognizing why basic locks may not provide sufficient protection against determined intrusion.
How Lock Vulnerabilities Are Exploited
Lock bypass techniques take advantage of how internal lock components are designed to respond to the correct key. Instead of breaking the lock, these methods rely on influencing internal parts so they momentarily behave as though a legitimate key is present.
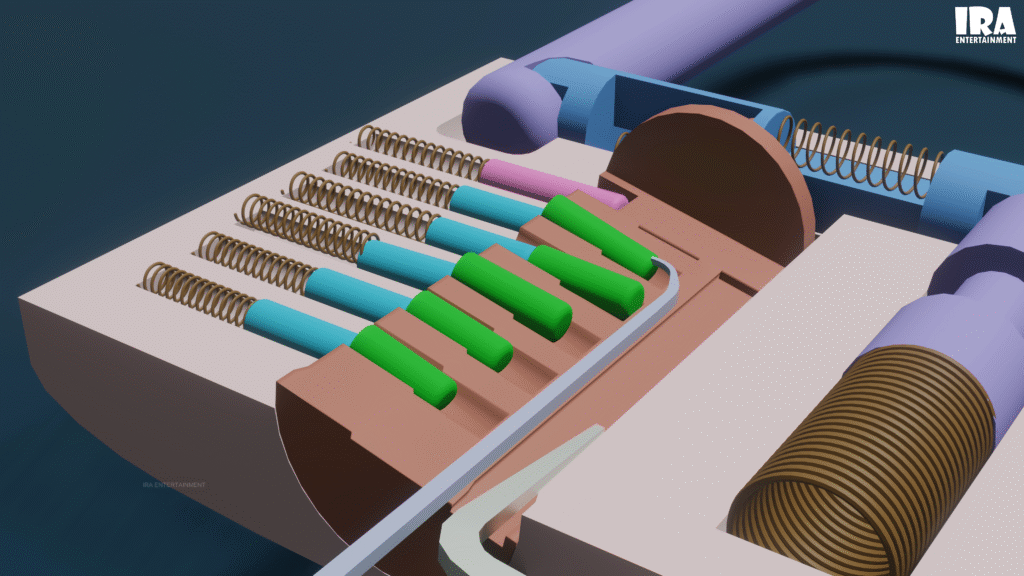
In basic pin tumbler locks, internal components are held in place by springs and must align precisely for the lock to turn. When rotational stress is applied during security testing or analysis, small mechanical imperfections may cause certain internal parts to respond before others. This uneven response can create brief moments where the lock mechanism becomes vulnerable.
When all internal components reach their intended alignment at the same time, the locking cylinder can rotate freely. This behavior highlights a core limitation of simpler lock designs and explains why many security professionals recommend stronger, more advanced locking systems for residential protection.
Rapid Lock Bypass in Low-Security Designs
In discussions about lock security, certain rapid bypass methods are often mentioned to illustrate the limitations of low-security pin tumbler locks. These references are used to explain how simpler internal designs may respond unpredictably when subjected to sudden internal disturbance during security testing or analysis.
In basic locks with minimal protective features, internal components can occasionally align momentarily due to their simplicity and loose tolerances. This behavior does not occur reliably and depends heavily on the quality, precision, and design of the lock. Higher-quality locks are specifically engineered to prevent this kind of temporary alignment through improved materials and advanced internal mechanisms.
This vulnerability highlights why low-cost, mass-produced locks may offer limited resistance and reinforces the importance of choosing locks designed with modern security threats in mind.
Why This Matters for You
Your home security may be weaker than you think. A lock that looks solid might only offer an illusion of safety. Burglars are often skilled at bypassing standard locks, using tools that can pick, bump, or manipulate doors in seconds. Understanding this reality is the first step toward truly protecting your home.
If you want better protection, start by upgrading your locks. High-security anti-pick locks are specifically designed to resist lockpicking, drilling, and other common break-in methods. These locks use advanced internal mechanisms, such as rotating pins or sidebar designs, making it much harder for intruders to force entry. While they might cost more upfront, they provide peace of mind that standard locks cannot.
Smart locks are another option for modern security. With features like fingerprint recognition, digital keypads, or remote access via smartphone apps, smart locks allow you to control who enters your home and when. Many models can alert you if someone attempts to tamper with them, giving you real-time awareness of potential threats. Even if you prefer traditional keys, pairing smart locks with high-quality deadbolts and restricted keyways can significantly reduce vulnerability. Restricted keyways prevent unauthorized duplication of keys, ensuring that only authorized individuals have access.
Physical barriers remain an important part of home security. Security bars on windows, reinforced doors, and sturdy gates can deter intruders and delay forced entry long enough for authorities to respond. Installing security cameras, motion sensors, or video doorbells adds another layer of protection. Not only do they serve as a deterrent, but they also allow you to monitor your home remotely and gather evidence if a break-in occurs.
While investing in hardware is critical, knowledge is your most powerful tool. Understanding how locks work — and how easily some can be picked or bypassed — empowers you to make informed decisions about your home’s protection. Many homeowners assume their locks are secure, but even high-quality locks can be vulnerable if paired with weak doors, poorly installed frames, or neglected entry points. Taking a holistic approach to home security — combining strong locks, smart technology, and physical reinforcements — is the key to creating a safe and resilient environment.
Finally, don’t underestimate the value of vigilance and habits. Simple measures like locking doors and windows consistently, avoiding hiding spare keys in obvious places, and being mindful of who has access to your home can dramatically improve security. Neighbors, family members, and trusted friends can form a supportive network, helping watch over your property when you’re away.
In essence, protecting your home is about combining technology, quality hardware, and awareness. A strong lock is just one part of the equation; education, preparedness, and proactive steps make up the rest. By taking the time to understand vulnerabilities, upgrade defenses, and monitor your surroundings, you turn your home into a space that’s truly secure — giving you peace of mind and safeguarding what matters most.
About the Author
This article was prepared by the IRA Studios editorial team, creators of high-quality 3D educational visualizations designed to simplify complex ideas through clear and engaging visuals.
Watch the Full 3D Animation
To explore all of these processes in 3D, check out our detailed 3D Animation video.
Watch it in Malayalam
Want to learn more through visual storytelling? Check out our detailed 3D explanation blog on How Does a Lock Work? Pin Tumbler Lock | 3D Visual Explanation
Useful Link